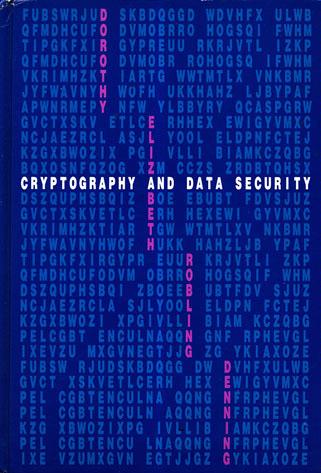
Cryptography and Data Security
by Dorothy Elizabeth Robling Denning
Publisher: Addison-Wesley 1982
ISBN/ASIN: 0201101505
ISBN-13: 9780201101508
Number of pages: 419
Description:
The goal of this book is to introduce the mathematical principles of data security and to show how these principles apply to operating systems, database systems, and computer networks. The book is for students and professionals seeking an introduction to these principles.
Download or read it online for free here:
Download link
(19MB, PDF)
Similar books
 Forensic Analysis of Database Tampering
Forensic Analysis of Database Tamperingby Kyriacos E. Pavlou, Richard T. Snodgrass - University of Arizona
The text on detection via cryptographic hashing. The authors show how to determine when the tampering occurred, what data was tampered, and who did the tampering. Four successively more sophisticated forensic analysis algorithms are presented.
(21236 views)
 The Developer Highway Code
The Developer Highway Codeby Paul Maher, Alex Mackman - Microsoft Press
This handbook summarises the principal security activities which should be a part of software development processes. It includes identifying security objectives, threat modelling, security design guidelines, security architecture reviews, and more.
(19252 views)
 Security Concepts
Security Conceptsby Travis H. - subspacefield.org
This is an online book about computer, network, technical, physical, information and cryptographic security, illustrated with interesting examples. It is not intended to be an introductory text, although a beginner could gain something from it.
(11716 views)
 Forensic Discovery
Forensic Discoveryby Dan Farmer, Wietse Venema - Addison-Wesley Professional
Forensic information can be found everywhere you look. The authors develop tools to collect information from obvious and not so obvious sources, walk through analyses of real intrusions in detail, and discuss the limitations of their approach.
(18422 views)